Gizmo Security
Customer data privacy and security are our biggest priorities. Below is a rundown of the various parts of our infrastructure and how the data is encrypted at each point.
GSX Gizmo cannot access the content of users’ emails or mailboxes other than the service accounts provided for the monitoring.
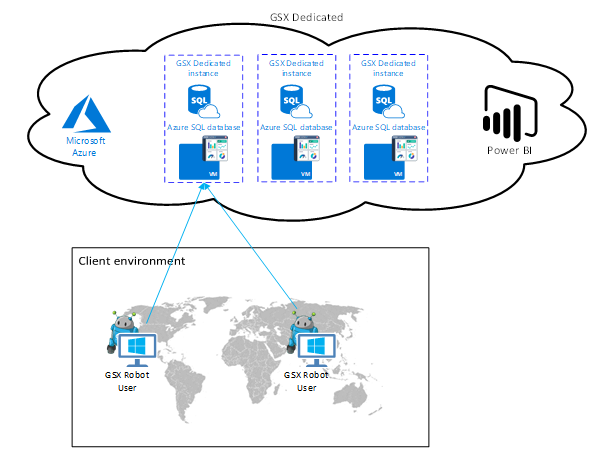
General Architecture
The GSX Gizmo front-end web servers redirect all visitors to a forced SSL (HTTPS) connection to prevent the transmission of customer data in plain text. All traffic between the user’s web browser and our web server is encrypted and secured with Azure Application Gateway. All our Azure infrastructure is secured with Firewalls, Multi Factor (MFA) and Azure Just in Time VM Access (JIT) authentication are implemented.
Data and encryption mechanisms
Passwords
All passwords are kept in memory encrypted and decrypted on-demand. We have implemented Symmetric encryption in AES-256, uniquely salted in Cipher Block Chaining (CBC).
Anonymization
GSX Gizmo does not retrieve any personal information in the monitored Office 365 tenant. The only personal information stored is the provided user accounts used for the performance monitoring and service health incidents retrieved from Microsoft.
Data retrieval
All data is collected from Microsoft’s servers is done over HTTPS. GSX Gizmo uses the Service Communication API to retrieve Service Health dashboard information. All the User Experience data is collected through client connections, relying on the native Microsoft client products so effectively using MAPI over HTTPS, HTTPS, EWS/HTTPS to connect to the various Office 365 workloads.
Data at rest
Data is encrypted at rest using military-grade encryption (AES-256). Each client data is logically separated in our back-end databases and is only accessible by senior GSX Administrators with your explicit consent.
There is different type of data stored and however please note that no Personally identifiable information (PII) is stored:
Results from scan (typically a date, unique identifier, statistic id, value)
Credentials for performing synthetic transactions (typically a dedicated user account for the monitoring aith regular “user rights”).
(Optional) Service accounts for accessing monitored servers or third party system that Gizmo integrates with.
Fully qualified domain names (FQDN) for each of the installed Robot Managers.
Robot Manager communication and encryption
The machine where the Robot Manager is installed must have a Certificate under the Computer Local Certificates. In the case it does not exist, the Install.ps1 file generate a new self-signed certificate with a key length of 2048 bit. Its public key is sent within the registration message to the RabbitMQ Bus.
This will enable the encryption of the parameters (or the whole message) sent to the Robot Manager by the Gizmo Scan Configuration Service.
The encryption mechanism is implemented with PGP - which is normally used to encrypt data being transferred over the network. It uses the concept of Public/Private keys based on a certificate. For more information on PGP: https://www.makeuseof.com/tag/pgp-me-pretty-good-privacy-explained/
Credentials needed
In order to monitor the end user experience for the various Office 365 workload GSX Gizmo requires one or several User Accounts with valid Office 365 license.
On top of the user account(s), GSX Gizmo should be provided with an Office 365 Service administrator in order to be able to retrieve events from the Service Health Dashboard. This service account cannot make any changes to your Office 365 tenant.
These credentials’ passwords will be encrypted as detailed above.
Internet Protocol Version 6 (IPv6)
Gizmo application is IPv6 compliant and we continuously ensure that the components are supporting this over time.